Automate and Elevate with Governance 360
InfoSec Governance
Don’t just manage your governance… master it. Finosec will help you translate difficult regulatory protocols into clear, actionable steps. Our platform optimizes every facet of your governance, ensuring you stay aligned, informed and proactive.
User Access Reporting
Managing who has access to what, when and how is stressful. Our User Access Reporting solution emphasizes clarity, security and simplicity. Let’s streamline your data security compliance and make it easier for your institution to maintain both accessibility and security.
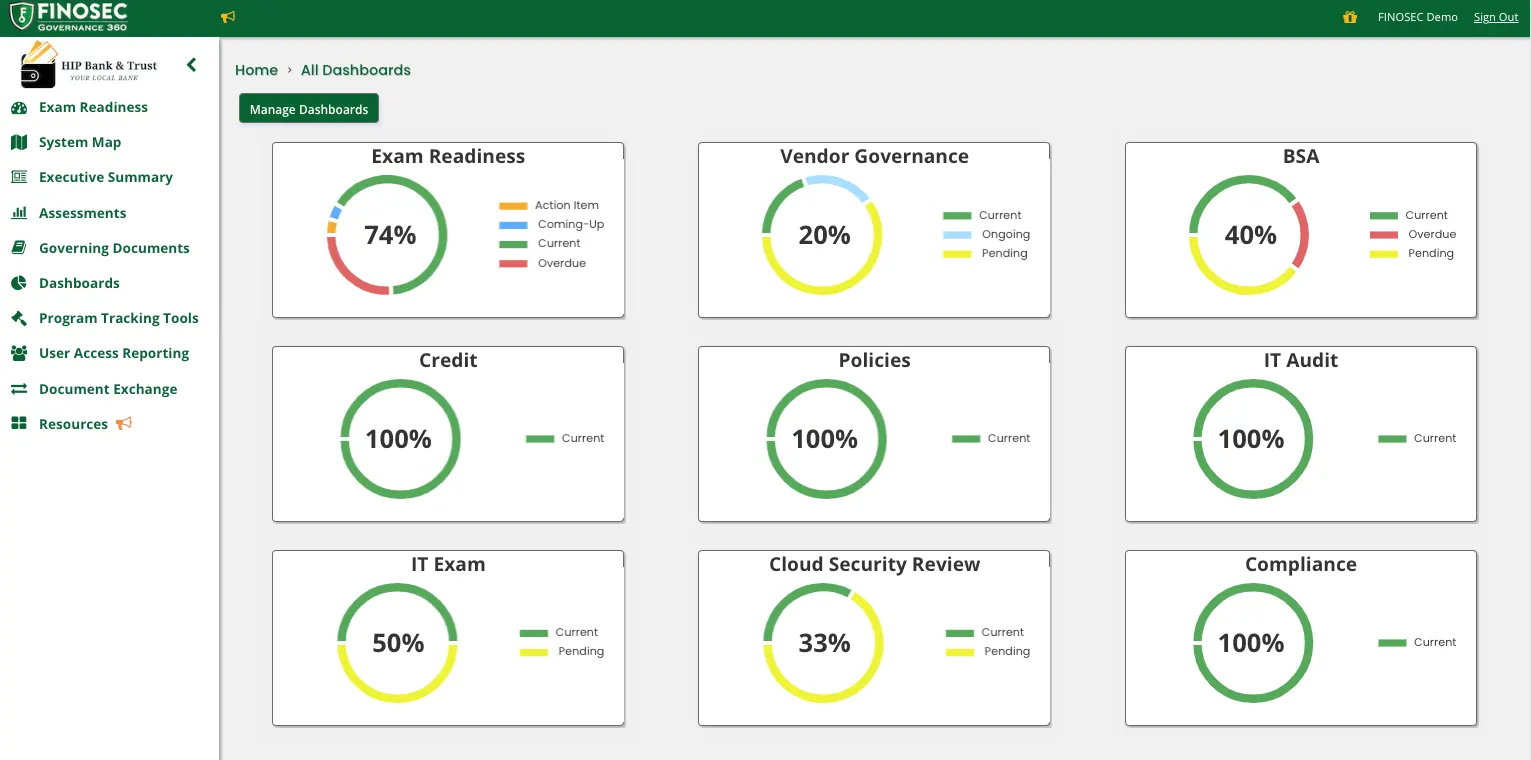
Gain a 360° View of Your Compliance
Keeping up with the ever-changing regulations, risks and requirements in the financial industry is a huge challenge for banks and credit unions. But with Finosec in your corner, your institution will tread new ground instead of just treading water.
We built our compliance automation software to help institutions of all sizes simplify and automate the governance process—so they can focus on their core business. At the heart of our cutting-edge solution is a transformative approach to user access review and a groundbreaking strategy for cybersecurity governance.
With Finosec as your compliance partner, you’ll:
- Watch your cumbersome tasks morph into smooth workflows, thanks to our compliance automation
- Document your systems and the crown jewels you need to protect
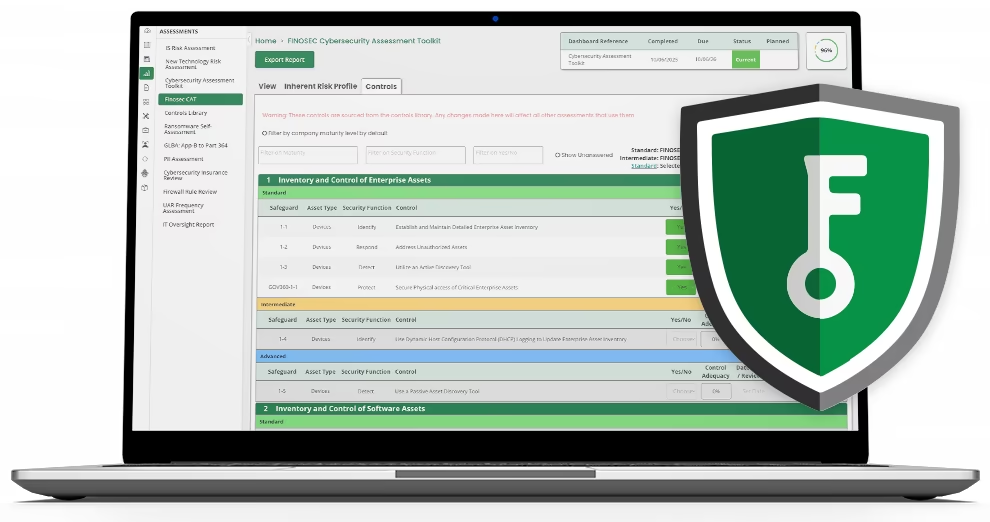
- Kickstart your compliance risk assessment with automated tools
- Plan your action items and set clear target dates
- Delegate tasks effortlessly, ensuring the right team member handles the right challenge
- Enjoy the comfort of real-time insight, always knowing where you stand in exam readiness and compliance stature
Simplify
Trouble with User Access Reviews?
View the case study to see how Finosec optimized user access reviews for South Atlantic Bank.
From the Blog
Compliance Solution or Governance Program? How to Tell What You Actually Have
After years of audits, exams, and evolving regulatory pressure, most financial institutions have something in place to manage compliance: tools, processes, and documentation. On paper, it works, but if you step back for a moment, a different question starts to...
Compliance vs. Governance: Why Checking the Box Isn’t Running the Program
For most bank IT and Information Security leaders, compliance isn’t just part of the job, it is the job. There’s always something coming up. An exam, an audit, or a request for documentation.So the focus becomes simple: make sure everything is in place, everything is...
Finosec Crosses 100+ ICBA Bank Mark, Accelerating Governance Modernization
Milestone reflects growing shift among community banks toward structured, scalable cybersecurity governance Finosec, a leading governance platform for financial institutions, today announced that more than 100 Independent Community Bankers of America (ICBA) member...

Beyond the CAT: Why Executive Reporting Matters More Than Ever for Community Banks
When the FFIEC CAT was sunset, it did more than create a gap in tooling; it created a gap in communication. The true value of the CAT was not just in the questions it asked, but in the structured way it enabled institutions to clearly communicate cybersecurity risk to...
From Legacy Spreadsheets to Boardroom Clarity
No thanks, I’ll re-enter my data manually